April 12, 2026
Virtual Desktops for Windows: A Guide for Canadian SMBsExplore virtual desktops for windows. Our guide compares AVD, Windows 365, and VDI for Canadian SMBs, covering security, cost, compliance, and implementation.
Read Full Post%20(1).webp)
Usman Malik
Chief Executive Officer
April 5, 2026
A managed firewall service provides your business with 24/7 expert monitoring and management over your network's primary defence. It’s what turns a firewall from a passive, digital wall into a proactive security shield that actively stops threats before they can do any real damage.
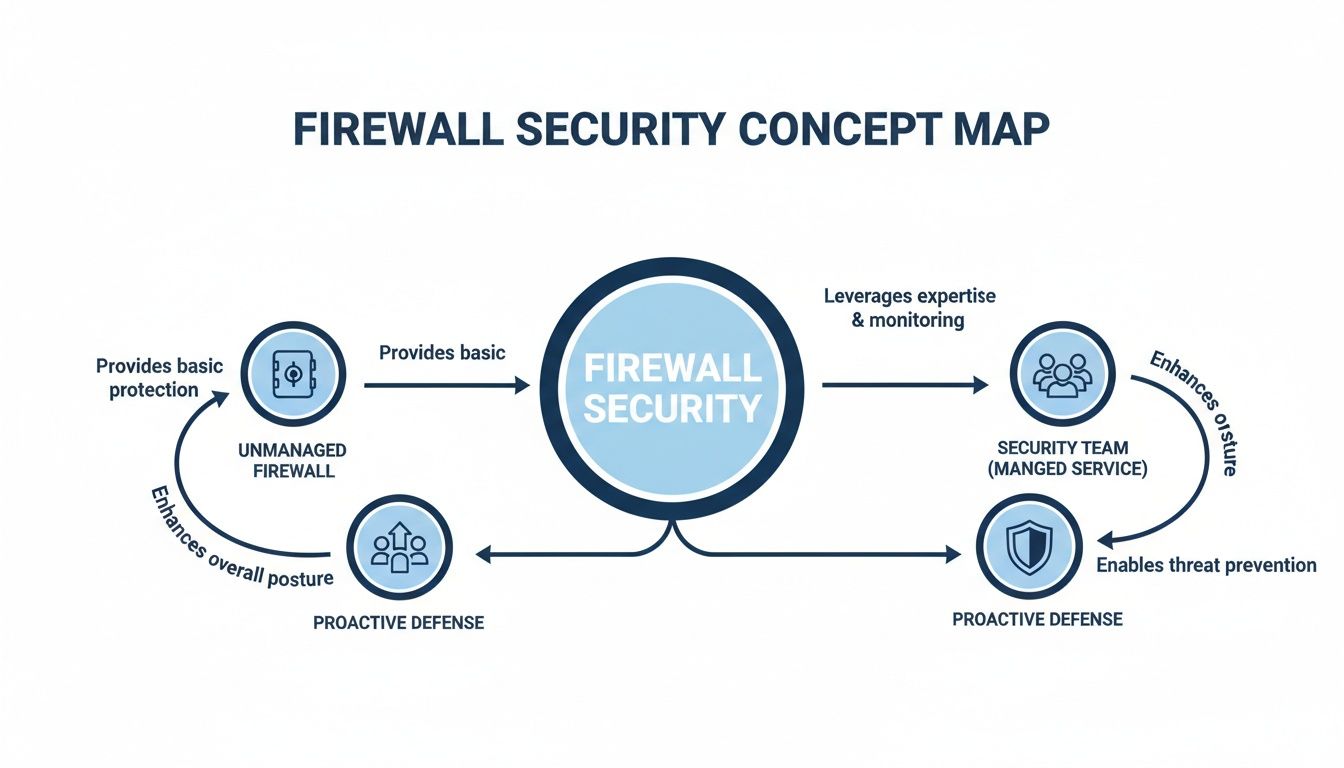
Picture your business network as a high-value vault. A standard, unmanaged firewall is the locked door—it offers a basic barrier, but who's watching the cameras? Who is checking the logs, updating the lock, and ready to respond if someone tries to pick it?
Without that constant vigilance, a locked door provides a false sense of security. This is exactly where managed firewall services come in. Instead of a "set-it-and-forget-it" device, you get a dedicated, 24/7 security team focused entirely on monitoring every entry point to your digital vault.
A managed service isn’t just about having a firewall; it's about making sure that firewall is working for you. For Canadian medium-sized organizations, that difference is critical. Cyber threats aren't static—they evolve daily, and an unmanaged firewall can become outdated in weeks, leaving your business wide open.
A managed firewall provider ensures your defences are always one step ahead by:
This proactive approach turns your network security from a potential liability into a genuine business asset.
For many organizations, the biggest risk isn't one specific threat, but the lack of dedicated resources to manage it. A managed firewall service bridges this gap, providing enterprise-grade expertise that most medium-sized businesses couldn't afford to hire in-house.
Outsourcing this function is a smart, strategic decision. It frees up your internal IT team to focus on projects that drive business growth, rather than spending their days putting out security fires. To see how this piece fits into a bigger picture, exploring the various modern cloud security services available can show you how to build a complete security strategy.
Ultimately, investing in managed firewall services is an investment in business continuity. It’s about protecting your data, keeping your operations online, and securing your company's hard-won reputation. For any modern business, this isn’t a luxury—it’s a necessity.
Let's break down how a managed firewall service operates. Think of your network’s entry point like the front door to your office building. An unmanaged, off-the-shelf firewall is like a standard lock on that door. It’ll stop someone from just walking in, but it won’t do much against a determined intruder with the right tools.
A managed firewall service, on the other hand, is like having a dedicated security team at that front door, 24/7. This team isn’t just watching who comes and goes; they’re actively vetting every person, checking IDs, screening packages, and monitoring all entrances and exits. They have the training and technology to spot trouble long before it reaches your office.
This is the fundamental shift: from a passive lock to a proactive, expert-led security operation.
The real work happens behind the scenes, combining powerful technology with the constant oversight of a remote Security Operations Centre (SOC).
Your managed service provider (MSP) deploys a suite of sophisticated tools that go far beyond a simple firewall. The goal is to create layers of defence that can identify and neutralize threats automatically.
Here’s a look at what’s running in the background:
A key strategy here is applying network segmentation best practices. This involves using firewalls to create secure, isolated zones within your network. If a breach somehow occurs in one area—say, the guest Wi-Fi—the firewall acts as a locked door, preventing the threat from spreading to critical areas like your finance department or server room.
All this technology is powerful, but it's the human element that truly makes the service "managed." A team of certified security analysts works around the clock, making the system intelligent and adaptive.
This team’s responsibilities are what separate a managed service from a DIY approach:
The real power of a managed firewall lies in its ability to adapt. An unmanaged firewall’s rules are static until someone manually updates them. A managed service, however, evolves in real-time as new threats emerge across the globe.
The results of this hands-on approach speak for themselves. With cyber threats escalating, Canadian businesses have seen a 28% rise in phishing attempts. Firewalls managed by experts successfully stop 92% of these attacks, a stark contrast to the 65% success rate of self-managed systems. This is especially important as North America now holds a 39.17% share of the global managed security services market.
It's this blend of smart technology and dedicated human expertise that delivers true peace of mind. For a broader view of how these services fit into a complete security strategy, check out our guide to security managed services.
Let's move beyond the technical jargon. What does a managed firewall service actually do for your business in the real world? The true value isn't just about blocking cyberattacks; it's about turning that advanced security into a strategic asset that strengthens your entire operation.
For many medium-sized organizations, this service isn't just another line item—it's a cornerstone of growth and stability. It shifts your firewall from a forgotten piece of hardware in a closet to a dynamic defence managed by experts, letting you get back to what you do best.
Think of an unmanaged firewall as a locked door. It's a good start, but it won't stop a determined intruder. A managed firewall, on the other hand, is like having a dedicated security team watching that door 24/7. This expert oversight brings immediate and tangible security improvements.
Your provider ensures security patches are applied the moment they’re released, threat intelligence is constantly updated, and firewall rules are fine-tuned to block the latest attack methods. This proactive management drastically shrinks your attack surface, hardening your defences against everything from common malware to sophisticated, targeted campaigns.
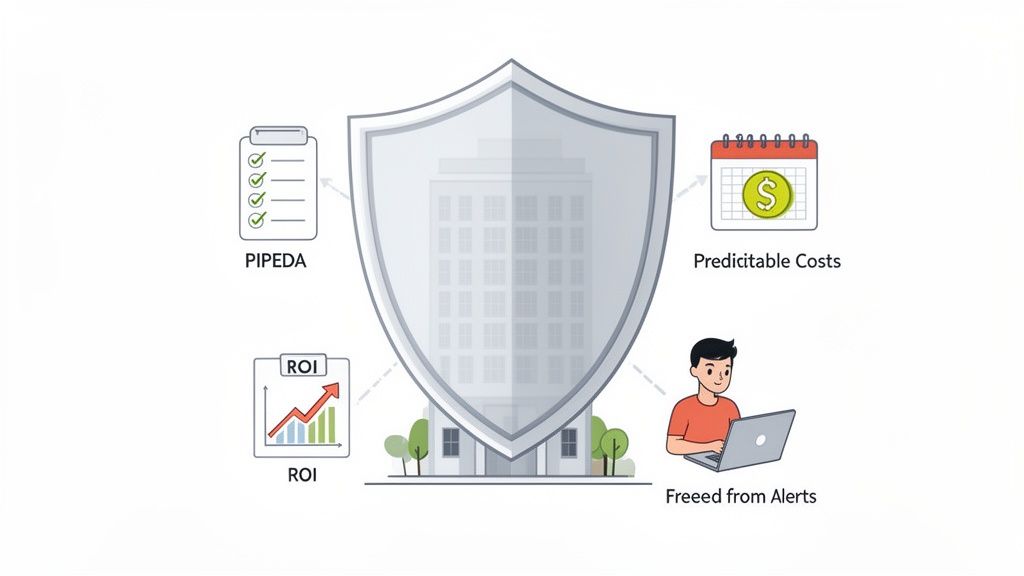
For any Canadian business, navigating regulations like PIPEDA isn't optional. Proving you're compliant means more than just having security tools; it requires active management and meticulous documentation. That’s a heavy lift for most internal IT teams.
A managed firewall service makes this much simpler by providing:
By handing this off, you gain a partner who lives and breathes compliance. This turns a complex headache into a managed process and is a key reason our clients find our broader cybersecurity services so critical for their operations.
One of the biggest wins for your business is swapping unpredictable capital expenses and potential breach costs for a fixed, predictable monthly fee. Managing a firewall in-house comes with all sorts of hidden costs, from staff training and emergency fixes to the high salary of a dedicated cybersecurity specialist.
A managed firewall service isn't an expense; it's an investment in business continuity. The predictable monthly fee is a small price to pay to avoid the devastating and unpredictable costs of a data breach, which include regulatory fines, legal fees, customer loss, and severe reputational damage.
The ROI becomes even clearer when you factor in the cost of downtime. A single hour of a network outage can cost a medium-sized business thousands in lost revenue and productivity. With a managed service backed by a solid Service Level Agreement (SLA), your provider is financially motivated to keep you secure and online, 24/7.
This financial stability is a major driver of adoption in Canada. Shifting to managed services can reduce in-house IT overhead by up to 40%, a critical factor for any business looking to optimize its budget. Considering that Canadian organizations faced over 2,500 significant cybersecurity incidents in 2025, the fact that professionally managed firewalls blocked 85% of initial intrusion attempts speaks volumes. This trend is part of why North America holds a dominant 39.17% global revenue share in the managed security market—business leaders are choosing this path for enterprise-grade protection so they can focus on growth. You can explore more about this growing market in this detailed industry report.
Picking a partner for your managed firewall services is just as important as the firewall technology itself. The wrong choice can lead to frustrating communication gaps and, even worse, security holes. But the right partner acts like a natural extension of your own team, giving you confidence in your security.
This isn't just another vendor contract; it's a long-term security partnership. You need to look past the sales pitch and dig into how they actually deliver their service. You’re looking for a provider who has the technical chops, of course, but who also understands what you’re trying to achieve as a business.
To help you make a confident decision, we've put together a checklist you can use to systematically vet potential providers. The table below outlines key criteria and questions to ask, ensuring you cover all your bases—from technical capabilities to their understanding of your specific business needs.
Use this checklist to systematically evaluate potential managed firewall service providers to ensure they meet your organization's security, compliance, and operational needs.
| Evaluation Criteria | Key Questions to Ask | What to Look For |
|---|---|---|
| Service Level Agreement (SLA) | What are your guaranteed response and resolution times for a critical incident? What are the penalties if you miss these targets? Do you guarantee network uptime? | A detailed, transparent SLA with specific, measurable metrics (e.g., "99.99% uptime," "15-minute response time for critical alerts"). Vague promises are a red flag. |
| Security Operations | Do you operate a 24/7/365 Security Operations Centre (SOC)? Where is your SOC located? Are your security analysts certified? | A 100% Canada-based SOC is crucial for data residency and compliance with laws like PIPEDA. The team should be available around-the-clock, not just during business hours. |
| Threat Intelligence | How do you stay ahead of emerging threats? What threat intelligence feeds do you use? Can you provide examples of how you've used this to protect clients? | Evidence of a proactive approach using multiple, reputable threat intelligence sources. They should be able to explain how this information translates into concrete protection for you. |
| Reporting & Transparency | Can we see a sample report? How often will we receive reports? What insights do they provide? | Clear, easy-to-understand reports that offer meaningful insights, not just a data dump. Look for analysis of threat trends, firewall performance, and security posture improvements. |
| Compliance Expertise | What experience do you have with our industry's regulations (e.g., HIPAA, PIPEDA, Law 25)? How do you help clients prepare for and pass audits? | Proven experience in your specific sector. They should be able to articulate exactly how their firewall policies and documentation support your compliance requirements. |
| Support & Communication | Who is my main point of contact? What is the escalation process for a major issue? | A dedicated account manager or a clear communication plan. You need to know exactly who to call and what to expect when a problem arises. |
After using this checklist to narrow down your options, you'll have a much clearer picture of which provider truly aligns with your organization's goals and security requirements.
The Service Level Agreement (SLA) isn't just paperwork—it’s the provider’s promise to you, written down. A weak, vague, or non-existent SLA should be an immediate deal-breaker. A good SLA clearly defines their commitments in terms you can actually measure.
Here’s what you should be asking:
A solid SLA shows a provider has confidence in their people and their processes. Don’t settle for vague promises; look for hard numbers.
Cyberattacks don’t work 9-to-5, so your security monitoring can’t either. It's absolutely critical that any potential partner runs a 24/7/365 Security Operations Centre (SOC) for around-the-clock threat monitoring and response.
For Canadian businesses, the location of that SOC is just as important. A 100% Canada-based SOC ensures your data stays within our borders, and it means the support team has a deep understanding of local compliance rules like PIPEDA. It also guarantees you get support in your time zone without any frustrating communication hurdles.
A provider's SOC is the heart of its managed firewall service. It’s the difference between discovering a breach a week later and stopping an attack in its tracks at 3 AM on a Sunday.
An effective managed firewall service is built on clear communication and tangible results. Ask any provider you’re considering for sample reports. You should be able to quickly understand what they’re telling you about threat activity, firewall performance, and your company’s overall security health.
Just as important, confirm their experience with your industry’s compliance standards. A partner who already knows the ins and outs of healthcare, finance, or legal regulations will be much better at configuring firewall rules to meet those specific needs. This is a vital point to discuss when you're looking into an MSSP for your security services.
A provider worth their salt should be able to clearly explain how they help clients stay compliant and show you the kind of documentation they provide for audits. This expertise is what transforms a managed firewall from a simple security tool into a true business asset.
For businesses operating in tightly regulated sectors, a generic, out-of-the-box security setup is a major liability. Industries like healthcare, finance, and legal face unique compliance pressures where a one-size-fits-all firewall can leave dangerous gaps. This is precisely where an experienced managed firewall services provider becomes more than a vendor—they become a crucial partner.
By tailoring security controls to your sector’s specific rules, a managed firewall stops being just another tool. It becomes a system that actively reinforces your compliance and gives you a competitive edge. Think of it as the difference between a generic home alarm and a security system custom-built to protect the specific assets that your business depends on.
If you're in healthcare, protecting patient data isn't just a best practice—it's the law. You're navigating a complex web of federal and provincial privacy acts, like Ontario’s Personal Health Information Protection Act (PHIPA). One misstep can lead to crippling penalties and completely erode patient trust.
An expert managed firewall provider will tackle these challenges head-on by:
This focused approach ensures your network doesn’t just defend against attacks but also upholds the rigid privacy standards that modern healthcare demands.
In regulated industries, compliance isn't just about avoiding fines; it's about building trust. A managed firewall customized for your sector demonstrates a clear commitment to protecting client and patient data, which is a powerful differentiator in a competitive market.
Legal and financial firms are built on a bedrock of confidentiality. You handle incredibly sensitive information daily, from private financial records to privileged legal documents. A data breach here does more than just disrupt your operations—it can shatter your firm's hard-won reputation.
A managed firewall customized for these sectors zeroes in on protecting client data and intellectual property. This means configuring specific policies to block unauthorized data exfiltration, prevent access to high-risk websites, and meticulously log all network activity to create a solid audit trail for PIPEDA compliance. For firms that regularly test their defenses, it's vital to see how these controls hold up under pressure. You can read our guide on penetration test services to see how proactive testing validates your firewall's real-world effectiveness.
Across Canada, regulated sectors are increasingly turning to cloud-based managed firewalls. A recent trend reveals that 62% of mid-sized businesses in Ontario and Alberta have shifted to hybrid or cloud firewalls, cutting costs by around 35%. For healthcare and finance, this move allows secure integration with platforms like Microsoft 365 while blocking up to 95% of advanced persistent threats with AI-driven policies. This is part of a bigger picture where North America accounts for 35.72% of global revenue for Firewall-as-a-Service, showing just how high the demand is for scalable, compliant security. You can discover more about how the network security market is expanding on delloro.com.
You’ve picked your provider and are ready to get your managed firewall services up and running—so, what’s next? This is where you really see the difference between a simple vendor and a true security partner. A good onboarding process isn't about just flipping a switch; it’s a structured, transparent journey designed to fold advanced security into your business with as little disruption as possible.
The whole process is a collaboration from start to finish. It begins long before any hardware shows up at your door, ensuring the final setup is a perfect fit for your operational needs and security goals. This methodical approach takes the mystery out of the technical side and builds a strong foundation for a long-term partnership.
The journey kicks off with a comprehensive discovery phase. Your new security partner will work closely with your team to get a deep, practical understanding of your current IT environment. This isn’t a quick glance; it’s a meticulous review.
This initial phase involves:
This groundwork is absolutely essential. By understanding precisely what needs protecting, the provider can design a security strategy that actually supports your business instead of getting in the way.
Once the assessment is done, the next step is designing the firewall rules and security policies. This is a highly collaborative process where your business goals steer the technical configuration. Your provider’s job is to translate your operational needs into specific, actionable rules.
For example, a policy might be set up to prioritize traffic for your business-critical VoIP system to guarantee call quality. Another might block access to high-risk websites to prevent malware from ever reaching your network. You’re part of this conversation, making sure the rules make sense for how your team actually works.
The goal of policy design is to create a security framework that is both robust and practical. The best firewall configuration is one that provides maximum protection while being completely invisible to your employees during their day-to-day work.
With the policies defined, the deployment begins. An experienced provider will manage this stage to ensure a smooth transition with little to no downtime. This could involve installing new firewall hardware and carefully configuring it according to the design you both agreed on.
The deployment phase includes:
After the system goes live, the final—and most crucial—step is the handover to the 24/7 monitoring team. This isn't just a technical handoff; it's a complete knowledge transfer. The deployment team ensures the Security Operations Centre (SOC) analysts fully understand your unique environment and custom policies.
To learn more about how this continuous oversight works, you might be interested in our article on remote monitoring and management. This step ensures the team watching your network has all the context needed to respond effectively from the very first minute. From this point forward, you have a dedicated team of experts safeguarding your network around the clock, backed by a clear process for ongoing reporting and strategic reviews.
When exploring managed firewall services, many business and IT leaders have similar questions. It's a significant decision, so getting clear answers is crucial. Here are some of the most common queries we receive, along with straightforward, expert answers.
That's a great first step, but owning a firewall is only half the job. Think of it like buying a top-of-the-line security system for your building—it’s useless if no one is watching the monitors, knows how to spot real trouble, or can respond when an alarm goes off.
An unmanaged firewall can be out-of-date in just a few weeks, leaving security holes you won't even see. A managed service provides the expert team that works 24/7 to update policies, patch vulnerabilities, and instantly react to alerts, ensuring your most important defence is always ready for a fight.
Yes, and for most medium-sized businesses, it’s actually more cost-effective than trying to build the same capability in-house. Hiring a single, qualified cybersecurity expert is expensive, and one person can’t possibly monitor your network around the clock.
With a managed firewall service, you get an entire team of certified security analysts and enterprise-grade tools for a predictable monthly cost. When you compare that fixed fee to the devastating and unpredictable costs of just one data breach—from downtime and regulatory fines to lost customer trust—the value becomes incredibly clear.
A key benefit is taking the day-to-day security pressure off your internal team. Your input is vital during the initial discovery and setup, where we collaborate to make sure the firewall rules align perfectly with your business operations and goals.
Once we go live, however, our team handles all the heavy lifting. This means 24/7 monitoring, all updates and patching, and full incident response. Your team is freed from putting out security fires and can finally focus on strategic projects that actually grow the business, while you get clear, simple reports on your security posture.
Our onboarding is designed to be thorough but smooth, so there’s no disruption to your daily work. We start with a deep dive into your current IT environment, security needs, and business objectives.
From there, we build a strategic plan and configure the firewall policies specifically for your organization. Our experts manage the entire deployment, testing, and validation process. Once everything is running perfectly, we execute a seamless handover to our 24/7 Canada-based monitoring team, giving them all the context needed to protect you from day one. We keep you in the loop the entire time, making you a partner in your security, not just a customer.
Ready to stop "setting and forgetting" your network security? CloudOrbis delivers proactive, 24/7 managed firewall services that truly protect your business and let your team get back to focusing on growth.
Secure your operations and gain peace of mind. Visit us at CloudOrbis to learn more.
April 12, 2026
Virtual Desktops for Windows: A Guide for Canadian SMBsExplore virtual desktops for windows. Our guide compares AVD, Windows 365, and VDI for Canadian SMBs, covering security, cost, compliance, and implementation.
Read Full Post
April 11, 2026
IT Management Service: A Guide for Canadian BusinessesExplore our complete guide to an IT management service in Canada. Learn about models, pricing, compliance, and how to find the right partner for your SMB.
Read Full Post
April 10, 2026
Best Managed Service Providers Vancouver 2026Find the best managed service providers vancouver has to offer with our 2026 checklist. Evaluate MSPs on security, compliance, SLAs, and pricing.
Read Full Post